SOC 2 isn’t just another compliance checkbox. It’s a structured attestation framework that proves your service organization meets specific security and privacy standards—standards your enterprise clients won’t negotiate on. The American Institute of CPAs (AICPA) created SOC 2 to evaluate how service providers protect customer data through five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Security is mandatory. The rest? You pick based on what your organization actually does.
If you’re handling sensitive customer data, SOC 2 compliance isn’t optional anymore. Many enterprise procurement teams demand current SOC 2 reports as a condition of vendor engagement, making this a market-access requirement, not a nice-to-have. You’ll choose between Type 1 (point-in-time design assessment) or Type 2 (operational effectiveness over time). Most serious buyers want Type 2.
You need to understand three things right now: what controls you must implement, how long the audit takes, and what it costs. Those answers determine whether you’re ready to start or need to build your security foundation first.
What SOC 2 Certification Actually Means
SOC 2 isn’t technically a “certification” in the traditional sense. It’s an attestation report prepared by a licensed CPA firm after auditing your controls against AICPA’s Trust Services Criteria. The auditor doesn’t “pass” or “fail” you. They attest whether your controls exist, are designed properly, and operate effectively.
The AICPA developed this framework specifically for service organizations—companies that store, process, or transmit customer data. SaaS platforms, cloud providers, managed service providers, and data centers are prime candidates. If your business model involves handling someone else’s sensitive information, you’re in scope.
The framework rests on five Trust Services Criteria. You don’t implement all five unless your business requires it. You select the criteria that match your service commitments to customers.
The Five Trust Services Criteria
Security forms the foundation. It’s mandatory for every SOC 2 audit. This criterion covers protection against unauthorized access—both physical and logical. Think access controls, encryption, network security, and change management.
Availability measures whether your systems and data are accessible when customers need them. Uptime commitments, disaster recovery, monitoring, and incident response all fall here.
Processing Integrity ensures your systems process data accurately, completely, and on time. Data validation, error handling, and quality controls matter most.
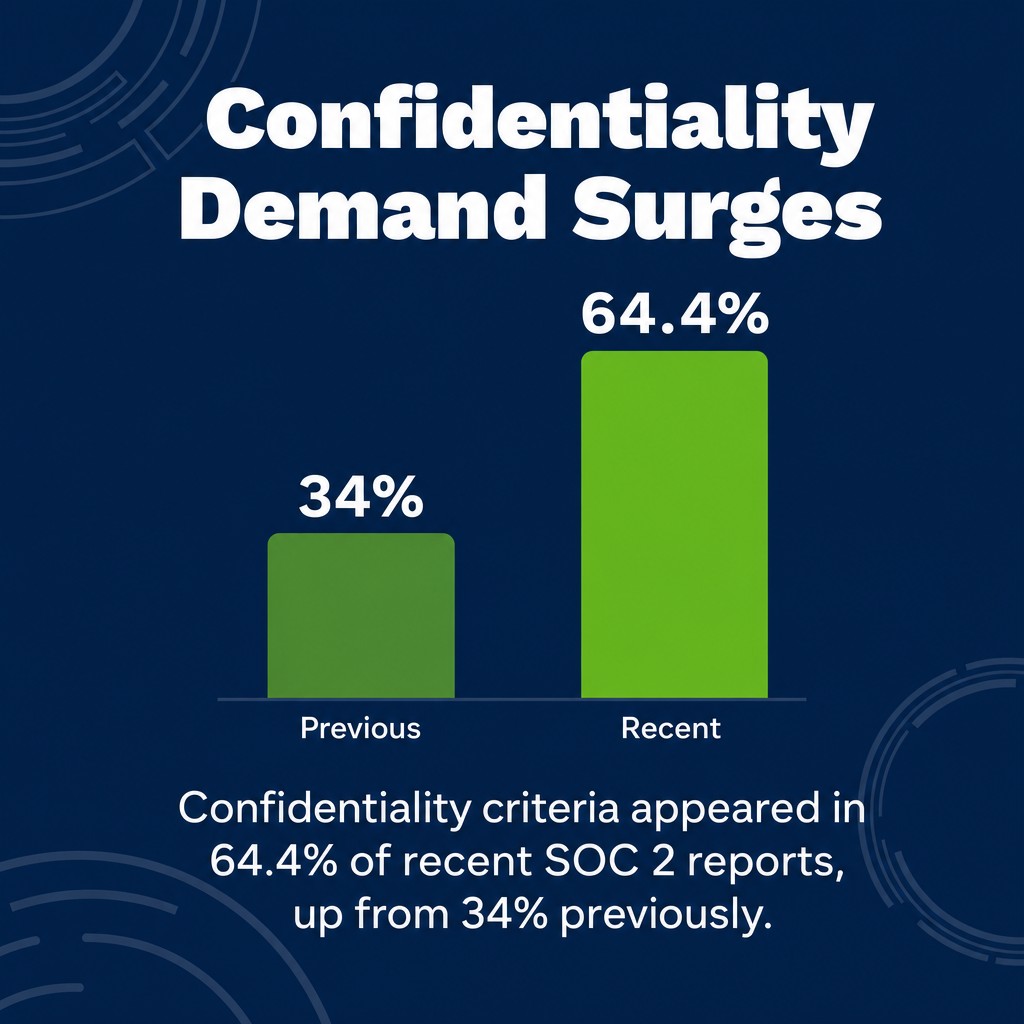
Confidentiality protects data designated as confidential. This isn’t the same as privacy. Confidentiality applies to proprietary business information, trade secrets, or data explicitly labeled confidential in your agreements. Confidentiality criteria appeared in 64.4% of recent SOC 2 reports, up from 34% previously, showing growing customer demands for this protection.
Privacy addresses personal information—how you collect it, use it, retain it, disclose it, and dispose of it. This criterion aligns with regulations like GDPR and CCPA but focuses on your specific privacy commitments.
Type 1 vs Type 2 Reports
Type 1 evaluates whether your controls are designed appropriately at a specific point in time. The auditor examines your policies, procedures, and control descriptions. They verify the controls exist and look sufficient on paper. That’s it. No testing over time.
Type 2 tests whether those controls actually worked over an extended period. The observation period typically spans at least three months, often extending to six or twelve months. Auditors collect evidence, test control execution, and document any exceptions or failures.

Enterprise buyers prefer Type 2. They want proof your controls function consistently, not just that they looked good during a one-day audit. Type 1 serves as a stepping stone—useful for demonstrating initial readiness or meeting immediate procurement requirements while you work toward Type 2.
| Aspect | Type 1 | Type 2 |
|---|---|---|
| Evaluation Focus | Control design at a point in time | Operating effectiveness over time |
| Observation Period | Single day assessment | 3-12 months of testing |
| Evidence Required | Policies and procedures documentation | Ongoing proof of control execution |
| Market Acceptance | Limited—often not sufficient for enterprise buyers | Standard requirement for vendor assessments |
Who Needs SOC 2 Compliance
Your customer data determines whether you need SOC 2. If third parties entrust you with their sensitive information, you need demonstrable controls. The framework exists for service organizations—businesses whose core offering involves data custody or processing for others.
SaaS companies top the list. If you sell software that stores customer data in your infrastructure, SOC 2 becomes a prerequisite for enterprise sales. HR platforms, CRM systems, financial software, healthcare applications—all handle data that demands third-party validation.
Cloud service providers and infrastructure hosts need SOC 2 by default. You’re literally storing other companies’ data on your servers. Your security posture directly impacts their risk profile.
Third-Party Vendor Management Requirements
Enterprise risk management programs mandate vendor assessments. Security teams evaluate every supplier that touches customer data. They request SOC 2 reports during procurement and renewal. Without one, you don’t make the approved vendor list.
With breach prevalence at 52% among organizations, buyers won’t take your word on security. They need independent verification from a qualified auditor. SOC 2 provides that verification in a standardized format.

Regulated industries impose even stricter requirements. Financial services, healthcare, and government sectors often require SOC 2 as a baseline. Some add specific control requirements beyond the standard framework.
Competitive Advantage in the Market
SOC 2 removes friction from sales cycles. Prospects trust third-party attestation more than your security questionnaire responses. You close deals faster when you can share a current report.
It signals maturity. Startups with SOC 2 compete against established players on security posture. You demonstrate you’ve invested in proper controls, not just moved fast and broken things.
Marketing benefits matter too. You can display trust badges, list SOC 2 in procurement portals, and differentiate from competitors who haven’t invested in compliance. Just don’t call it “certification”—auditors will correct that terminology quickly.
The SOC 2 Audit Process Explained
SOC 2 audits follow a structured path. You can’t skip steps. The process begins long before the auditor shows up and continues well after they leave.
First, you scope the audit. Which Trust Services Criteria apply to your business? What systems and processes fall in scope? Where’s your data? Who has access? Clear boundaries prevent scope creep and control audit costs.
Then you select your auditor. SOC 2 audits must be conducted by licensed CPA firms registered with appropriate state boards and maintaining active AICPA membership. Big Four firms cost more but carry brand recognition. Mid-tier firms often provide better service and responsiveness. Choose based on your industry, complexity, and budget.
Readiness Assessment and Gap Analysis
Smart organizations run a readiness assessment before the formal audit. You document current controls, identify gaps, and build remediation plans. This prevents expensive audit delays when the CPA discovers you’re not actually ready.
The gap analysis maps your controls to the Trust Services Criteria. Where do you meet requirements? Where do you fall short? What evidence can you produce? Missing documentation kills audits faster than missing controls.
You’ll need comprehensive documentation: security policies, access control procedures, change management protocols, incident response plans, vendor management processes, and employee training records. If it’s not documented, it doesn’t exist from an audit perspective.
The Examination Period
Type 1 examinations happen quickly—often within a few weeks once you’re ready. The auditor reviews your control design, interviews key personnel, and verifies documentation. They’re not testing whether controls worked, just whether they’re properly designed.
Type 2 examinations take months because of the observation period requirement. Your controls must operate consistently throughout this window. The auditor tests samples, reviews logs, and validates evidence. They’re looking for control failures, exceptions, and gaps between what you documented and what you actually did.
Approximately 92% of organizations now conduct two or more SOC 2 audits annually, reflecting the shift from one-time certification to continuous compliance. The first audit is the hardest. Subsequent audits get smoother as you mature your processes.

Report Issuance and Distribution
The auditor produces your SOC 2 report after completing their examination. This document includes your system description, the Trust Services Criteria you selected, your control assertions, and the auditor’s opinion.
For Type 2, the report details testing procedures, results, and any exceptions. Clean reports show no control failures. Reports with exceptions explain what went wrong and how you responded.
You control report distribution. SOC 2 reports aren’t public documents. You share them under NDA with prospects and customers who need to assess your controls. Some organizations use bridging letters or summary documents for broader distribution.
SOC 2 Compliance Requirements Breakdown
The Security criterion forms the core of every SOC 2 audit. You can’t opt out. It addresses protection against unauthorized access—the fundamental expectation for any service organization handling customer data.
Access controls come first. Who can access what systems? How do you authenticate users? What about privileged access? Role-based access control (RBAC) maps permissions to job functions. Multi-factor authentication (MFA) protects critical systems. Regular access reviews ensure you revoke permissions when people change roles or leave.
Change management prevents unauthorized modifications to production systems. You need documented procedures for planning, testing, approving, and implementing changes. Separation of duties ensures the person who codes doesn’t deploy to production without approval.
Core Security Controls
Network security controls protect your infrastructure perimeter. Firewalls, intrusion detection systems, and network segmentation limit attack surfaces. You’ll document network architecture and prove you’ve implemented appropriate boundaries.
Encryption protects data in transit and at rest. TLS for network communications. Encrypted databases and backups. Key management procedures that prevent unauthorized decryption. Auditors will test encryption implementation and key protection.
Logging and monitoring detect security incidents. You need centralized log collection, retention policies, and active monitoring for suspicious activity. Your incident response plan documents how you detect, respond to, and recover from security events.
Additional Trust Services Criteria
Availability controls ensure uptime commitments. If you promise 99.9% availability, you need monitoring, redundancy, and disaster recovery capabilities to deliver it. Backup testing proves you can actually restore from those backups you’re creating.
Processing Integrity requires data quality controls. Input validation prevents garbage data. Error handling catches processing failures. Reconciliation procedures verify data accuracy across systems.
Confidentiality demands data classification and handling procedures. Which data is confidential? How do you label it? What restrictions apply to confidential data access, transmission, and storage?
Privacy controls map to your privacy notice. You must implement what you promise. Data collection minimization, consent management, retention schedules, and deletion procedures all need documented controls.
Timeline: How Long Does SOC 2 Take
The honest answer? It depends on where you’re starting from. A mature organization with existing controls moves faster than a startup building from scratch.
Readiness preparation typically takes three to six months for organizations with some security foundation. You’re documenting existing controls, filling gaps, and collecting evidence. Startups with minimal controls might need six to twelve months to build proper security programs.
Type 1 audits execute quickly once you’re ready—usually four to eight weeks from kickoff to report delivery. Type 2 audits add the observation period. Most organizations run six-month observation periods for their first Type 2 audit. This gives you time to demonstrate consistent control operation while keeping the timeline reasonable.
Factors That Affect Timeline
Organizational readiness matters most. If your controls already exist and you’ve got documentation, you’re months ahead of organizations starting from zero. Gap assessments reveal how ready you actually are.
Scope complexity extends timelines. Multiple systems, complex infrastructure, and numerous applications require more audit effort. Keep your initial scope focused. You can expand in future audits.
Auditor availability impacts scheduling. Popular audit firms book months in advance. Factor in their calendar when planning your timeline. Mid-tier firms often offer faster engagement starts.
Your internal resources determine execution speed. Audits demand significant time from your team. Someone needs to collect evidence, coordinate with auditors, and respond to findings. Understaffed organizations struggle to keep audits moving.
Accelerating the Process
Start with a gap assessment. Know what you’re missing before you engage the auditor. This prevents expensive delays when they discover you’re not ready.
Use compliance automation platforms. Tools like Vanta, Drata, and Secureframe map controls, collect evidence automatically, and maintain compliance dashboards. They don’t replace the audit but streamline preparation significantly.
Hire experienced consultants if you lack internal expertise. They’ve guided dozens of companies through SOC 2. They know what auditors expect and can prevent common mistakes.
Run Type 1 first if you need quick market access. Get the design validation while you work toward Type 2. This gives prospects something to review while you complete the observation period.
SOC 2 Certification Costs in 2026
Budget realistically. SOC 2 compliance costs more than most organizations expect—not because auditors are expensive (though they are), but because proper controls require investment.
SOC 2 certification costs for 2026 range from $5,000 to $20,000 for Type 1 audits and $8,000 to $50,000+ for Type 2. Small companies with simple infrastructure pay less. Complex enterprises with multiple systems and locations pay significantly more.
Audit fees represent only part of total costs. You’ll spend substantially more preparing for the audit than paying the auditor.
Total Cost of Compliance
SOC 2 total first-year compliance costs for small to mid-size SaaS companies range from $20,000 to $35,000. This includes audit fees, tools, consulting, and internal labor.

Compliance automation platforms form a major cost component. SOC 2 compliance automation platforms typically cost between $6,000 and $15,000 annually for small to mid-size organizations. These tools reduce manual effort but represent ongoing expenses.
Internal labor costs add up quickly. Your team will spend hundreds of hours on documentation, evidence collection, and auditor coordination. Calculate this at fully loaded employee costs.
Control implementation requires investment. Missing controls cost money to fix. You might need new security tools, infrastructure upgrades, or additional staff. A $10,000 security information and event management (SIEM) system isn’t optional if you lack centralized logging.
Ongoing Compliance Costs
SOC 2 isn’t one-and-done. Annual audit fees recur. Type 2 audit fees can be $8,000 to $12,000 for subsequent years once you’ve established your control environment.
Continuous monitoring requires sustained effort. Controls don’t maintain themselves. You need ongoing log reviews, access recertifications, vulnerability scanning, and policy updates.
Tool subscriptions continue annually. Budget for compliance platforms, security tools, and infrastructure as recurring operational expenses.
Consider the cost of non-compliance too. Lost deals hurt more than audit fees. If enterprise prospects require SOC 2 and you don’t have it, you’re losing revenue opportunities that dwarf compliance costs.
How to Prepare for SOC 2 Certification
Preparation determines audit success. Organizations that rush into audits waste money on delays, rework, and extended timelines. Those that prepare methodically complete audits smoothly.
Start by understanding your current state. What controls already exist? Where are the gaps? What documentation can you produce today? Honest assessment prevents false starts.
Document everything. Policies, procedures, system configurations, access controls, change logs—if you can’t prove it exists, the auditor can’t give you credit. Written policies that reflect actual practices matter more than theoretical security nobody follows.
Essential Preparation Steps
Define your scope boundaries carefully. Which systems store or process customer data? What applications fall in scope? Where’s the data? Clear scope definition controls costs and prevents audit expansion.
Implement the Security criterion controls first since they’re mandatory. Access management, encryption, change control, logging, monitoring, and incident response form your foundation. Don’t skip ahead to optional criteria until Security is solid.
Build your evidence collection process. You’ll need proof of control operation throughout the observation period. Automated evidence collection beats manual processes. Set up systems to capture access reviews, change approvals, log reviews, and training completion automatically.
Train your team on their control responsibilities. People execute controls. If they don’t understand what’s expected or why it matters, controls fail. Training records also provide audit evidence.
Common Preparation Mistakes
Don’t confuse policy with practice. Auditors test actual control operation. Beautiful policies that nobody follows fail audits. Implement realistic controls your team will actually execute consistently.
Avoid documentation overkill. You need sufficient documentation to demonstrate control design and operation. You don’t need 200-page policy manuals. Practical, concise documentation that people read and follow beats comprehensive documentation that sits unread.
Don’t neglect vendor management. Third-party service providers that handle your customer data create inherited risk. You need vendor contracts, security assessments, and monitoring controls. Many organizations discover vendor gaps during audits.
Test your controls before the auditor does. Run internal tests. Check whether logs exist. Verify backups actually restore. Find failures yourself and fix them before they become audit exceptions.
Maintaining SOC 2 Compliance
Getting SOC 2 is easier than keeping it. Controls require continuous operation. Evidence collection never stops. The observation period just shifts to a rolling window.
Continuous monitoring ensures controls keep functioning. Access reviews happen quarterly. Log monitoring runs daily. Vulnerability scanning executes weekly. You’re not preparing for an annual event—you’re maintaining an ongoing security program.
Control changes need documentation. When you modify systems, update procedures, or implement new security measures, document them properly. Changes without documentation look like control failures to auditors.
Annual Audit Cycles
Most organizations run annual SOC 2 audits. Your observation period rolls forward each year. The December report covers June through November. Next year’s report covers the following period.
Successive audits get more efficient. You’ve established your control environment. Documentation exists. Evidence collection is automated. The auditor knows your organization. Subsequent audits focus on changes and testing rather than building everything from scratch.
Budget for control maturity improvements. First audits often reveal opportunities to strengthen controls. Subsequent audits should show increasing maturity through enhanced automation, better monitoring, and stronger security posture.
When Controls Fail
Control failures happen. Systems go down. Someone grants inappropriate access. A change breaks something. The question isn’t whether you’ll have control failures—it’s how you respond when they occur.
Document incidents immediately. What happened? When? Who was affected? What did you do? Thorough incident documentation demonstrates your response capability even when the initial control failed.
Implement corrective actions. Fix the root cause. Update procedures to prevent recurrence. Test the fix. Auditors evaluate your response to control failures as much as the failures themselves.
Communicate transparently with your auditor. Hiding control failures ensures they become audit exceptions. Proactive disclosure with documented remediation shows mature risk management.
SOC 2 vs Other Compliance Frameworks
SOC 2 isn’t the only compliance framework service organizations encounter. Understanding how it relates to other standards helps you choose the right certifications and avoid duplicate effort.
ISO 27001 is the closest equivalent globally. It’s an international standard for information security management systems. ISO provides broader geographic recognition while SOC 2 dominates North American markets. ISO certifies your entire organization while SOC 2 focuses on specific service commitments.
Control overlap between ISO 27001 and SOC 2 is substantial. Organizations with ISO 27001 find SOC 2 easier. The control concepts align even though the frameworks differ. Some organizations pursue both to satisfy different customer requirements.
Industry-Specific Standards
HIPAA applies to healthcare organizations handling protected health information. SOC 2 doesn’t replace HIPAA but can complement it. Healthcare service providers often need both—HIPAA for regulatory compliance and SOC 2 for customer assurance.
PCI DSS governs payment card data security. If you process, store, or transmit credit card information, PCI compliance is mandatory regardless of SOC 2 status. Payment processors typically need both frameworks.
For more information on navigating multiple compliance requirements, see our guide to cybersecurity compliance requirements.
When Multiple Frameworks Make Sense
Different customers demand different certifications. Enterprise SaaS companies often maintain SOC 2, ISO 27001, and industry-specific certifications simultaneously. This isn’t redundant—each serves distinct market needs.
Build your compliance program to support multiple frameworks. Core security controls satisfy requirements across standards. Strong access management, encryption, logging, and incident response meet expectations everywhere.
Start with SOC 2 if you’re primarily serving North American enterprise customers. Add ISO 27001 for European markets or global enterprise prospects. Layer industry standards as specific customer requirements demand.
Choosing Your SOC 2 Auditor
Your auditor choice significantly impacts audit experience, cost, and timeline. Not all CPA firms are created equal for SOC 2 examinations.
Big Four accounting firms (Deloitte, EY, KPMG, PwC) offer brand recognition and deep expertise. Enterprise customers know these names. Audits conducted by Big Four firms carry weight in procurement decisions. You pay premium prices for that brand value.
Mid-tier and regional firms often provide better service and responsiveness for small to mid-size organizations. They have qualified auditors and AICPA membership. They understand SOC 2 requirements. They just charge less and move faster.
Auditor Selection Criteria
Verify proper licensing. The auditor must be a licensed CPA firm. Individual auditors need active CPA licenses. The firm requires AICPA membership and peer review. These aren’t optional qualifications—they’re legal requirements.
Evaluate industry experience. Has the firm audited organizations like yours? Do they understand your technology stack? Can they speak your language? SaaS companies need auditors who understand cloud architectures, not just traditional data centers.
Assess responsiveness and availability. You’ll work closely with your audit team for months. Slow responses and scheduling delays kill timelines. Interview potential auditors about their process, timeline, and communication approach before engaging.
Compare pricing structures. Some firms quote fixed fees. Others bill hourly. Understand what’s included and what triggers additional charges. Scope changes, extended timelines, and extra systems all increase costs.
Working Effectively With Your Auditor
Treat your auditor as a partner, not an adversary. They’re not trying to fail you. They’re attesting to the accuracy of your control assertions. Help them understand your environment.
Respond promptly to information requests. Audit delays usually stem from slow evidence provision, not auditor availability. Assign someone to coordinate audit requests and track responses.
Ask questions when you don’t understand requirements. Better to clarify expectations during the audit than discover misunderstandings in the final report. Good auditors want you to succeed.
Common SOC 2 Challenges and Solutions
Every organization hits obstacles during their first SOC 2 audit. Knowing common challenges helps you avoid or address them quickly.
Incomplete documentation kills more audits than missing controls. You implemented access reviews but didn’t record who reviewed what and when. You have change management but no approval records. You monitor logs but don’t document what you reviewed.
Solution: Build documentation into your processes from the start. Access review templates capture required information. Change management systems record approvals automatically. Log review checklists document monitoring activities. Make documentation a natural byproduct of executing controls.
Evidence Collection Struggles
Manual evidence collection becomes overwhelming during the observation period. You need quarterly access reviews for 50 systems. Monthly log reviews across multiple platforms. Evidence of hundreds of changes. Trying to collect this manually ensures failure.
Solution: Automate everything possible. Compliance platforms like Vanta and Drata connect to your systems and collect evidence automatically. They generate access review reports, capture security configurations, and document control execution without manual effort.
For organizations handling sensitive customer information, implementing proper data protection measures is essential. Learn more in our data privacy compliance guide.
Scope Creep and Control Gaps
Audits reveal controls you thought existed but don’t. That vendor security assessment process you described? Nobody actually executed it. The encryption you documented? Only implemented on some systems. Gap discoveries mid-audit force delays and remediation.
Solution: Run a thorough gap assessment before engaging your auditor. Test your own controls. Request evidence internally to verify it exists. Fix gaps during preparation, not during the audit. Consider a readiness assessment from the audit firm or a third-party consultant.
Resource Constraints
Small teams struggle with the time demands SOC 2 imposes. Your security engineer already has a full workload. Now they’re coordinating the audit, collecting evidence, and responding to findings. Something breaks.
Solution: Budget for the true time investment. Hire temporary help during the audit period. Bring in consultants who specialize in SOC 2 preparation. Defer non-critical projects during the observation period. Recognize that compliance is a business priority that requires dedicated resources.
Key Questions About SOC 2
How hard is it to get a SOC 2?
Difficulty varies with your starting point. Organizations with mature security programs and existing controls find SOC 2 achievable within six to nine months. Startups building controls from scratch face steeper challenges and twelve-month timelines.
The technical requirements aren’t impossible. The challenge lies in implementing controls consistently and documenting everything properly. Smaller teams struggle more with resource constraints than technical complexity.
Is SOC 2 required by law?
No. SOC 2 is a voluntary framework. No regulation mandates SOC 2 compliance. However, market forces often make it effectively mandatory for service organizations pursuing enterprise customers.
Some industries have specific regulatory requirements that SOC 2 can help address but doesn’t replace. Healthcare organizations need HIPAA compliance regardless of SOC 2 status. Financial services firms face regulatory oversight beyond SOC 2 scope.
Can I get SOC 2 certified myself or do I need an auditor?
You cannot self-certify SOC 2 compliance. The framework requires examination by an independent CPA firm. That’s the entire point—third-party validation that your controls meet standards.
You can prepare internally. You can implement controls, document procedures, and collect evidence without external help. But the final attestation report must come from a qualified auditor.
How often do I need to renew SOC 2?
SOC 2 reports don’t expire on a fixed schedule, but they lose value quickly. Most customers expect reports no older than twelve months. Enterprise procurement teams often require reports from the last six months.
Plan for annual audits. This maintains continuous compliance and ensures your reports stay current for customer reviews. The observation periods roll forward each year, creating ongoing compliance rather than periodic certification.
What happens if I fail a SOC 2 audit?
SOC 2 audits don’t use pass/fail language. The auditor issues an opinion on your controls. A clean opinion means controls are designed and operating effectively. A qualified opinion identifies control failures or limitations.
Reports with exceptions document what went wrong. Customers review these reports and decide whether the issues matter for their risk assessment. Some control failures are acceptable depending on severity and your response.

Next Steps: Starting Your SOC 2 Journey
You’ve got the information. Now execute.
Start with an honest gap assessment. Map your current controls to the Security criterion at minimum. Where are you solid? Where do gaps exist? What documentation can you produce today? This assessment determines whether you’re months away or need a year of preparation.
Define your scope precisely. Which systems must be included? What Trust Services Criteria apply to your service commitments? Focused scope accelerates your first audit. You can expand later.
Build your control documentation. Write down what you actually do, not what you wish you did. Document policies that reflect real practices. Create procedures people will actually follow. Record evidence of control execution systematically.
Consider tools that accelerate preparation. Compliance automation platforms reduce manual effort significantly. They’re not cheap, but they’re cheaper than failed audits and extended timelines. Evaluate options based on your systems and needs.
Understanding the broader context of security audits helps too. Read our article on benefits of regular cybersecurity auditsto see how SOC 2 fits into your overall security strategy.
Engage an auditor early. Get their input on your scope and readiness. Some firms offer pre-audit consultations. Use them. Finding issues before the formal audit begins saves time and money.
For service organizations, particularly those in cloud computing, implementing robust security measures is foundational. Our cloud security best practices guide covers essential controls that align with SOC 2 requirements.
SOC 2 compliance protects your customers’ data and opens enterprise market access. The investment pays off through faster sales cycles, higher close rates, and stronger security posture. The question isn’t whether to pursue SOC 2. It’s whether you’re ready to start now or need to build your foundation first.












